Now that all kinds of our sensitive personal information is recorded online – from various forms of instant messages, to banking records, to Snapchats – we’ve seen a series of high-profile scandals where huge databases of user passwords have been copied and shared around the internet. Back in 2011, for example, when the dating site Plenty of Fish had its database swiped, security experts were horrified that a site with 28 million users had dared to store its passwords in “plain text” – that is, unencoded – which was then described as the equivalent of “leaving the keys to the kingdom outside the moat.”
Statements published by McGill on September 11 and October 30 have raised questions about whether faculty and student passwords at the University are being stored using this same insecure method. In the statements, McGill IT Services publicly announced they would be “doubling” certain staff passwords. To use their example, “If your password is currently ‘McGill12,’ it will be changed to ‘McGill12McGill12.’”
The industry standard for secure password storage has for many years been a technique called a “salted hash.” Using this technique, your password is not stored anywhere, and the system only retains a “hash”: a string of binary numbers that results from running an irreversible cryptographic algorithm on your password. For example, if your password was “thisisdog2,” a particular algorithm might produce the hash “804410dcba8801f89b58c31f973e6b8e.” But, given enough hashes and passwords, the algorithm can be attacked by comparing passwords with hashes and thus the password could be exposed. To avoid this, developers add what they call a “salt” to the hashes. The salt adds a element to the password that randomizes the hashes, making it nearly impossible to identify the original password. Going back to the example of “thisisdog2,” first it would be salted: “[salt]thisisdog2” and then it would be hashed. Another password would have a different salt: for example, “supersecret” would be salted to become “[blue]supersecret.”
Insecure password storage is particularly ironic – and even hypocritical – given that IT Services is given to proselytizing the virtues of information security to its users.
When you enter your password to log in, the system just runs the same irreversible cryptographic algorithm (salt and hash) on the password you enter, and then checks to see if the output value matches the encoded version it already has stored in the database. The system only stores the salt and the resulting hash, never the original password that was typed in. That’s what makes the technique so secure – even the system itself does not know what your actual password is. This is why even if you forget your password, it can’t be sent back to you, because the system doesn’t know what it is, and can only be reset to something else. For the same reason, a hacker who would get access to the system would have great difficulty using it to discover what the passwords actually are.
So how could McGill be able to “double” passwords unless they are stored insecurely in the system as plain text?
In an email The Daily received from Ghilaine Roquet, McGill’s Chief Information Officer, she wrote that in her view, “McGill’s passwords are safe.” But she acknowledged that a “number of people have asked how we were able to double user passwords.” The answer is that although McGill uses encryption in certain parts of the password authentication process, a “legacy VPN infrastructure maintains its own data store,” and this data sits unencrypted on the storage device.
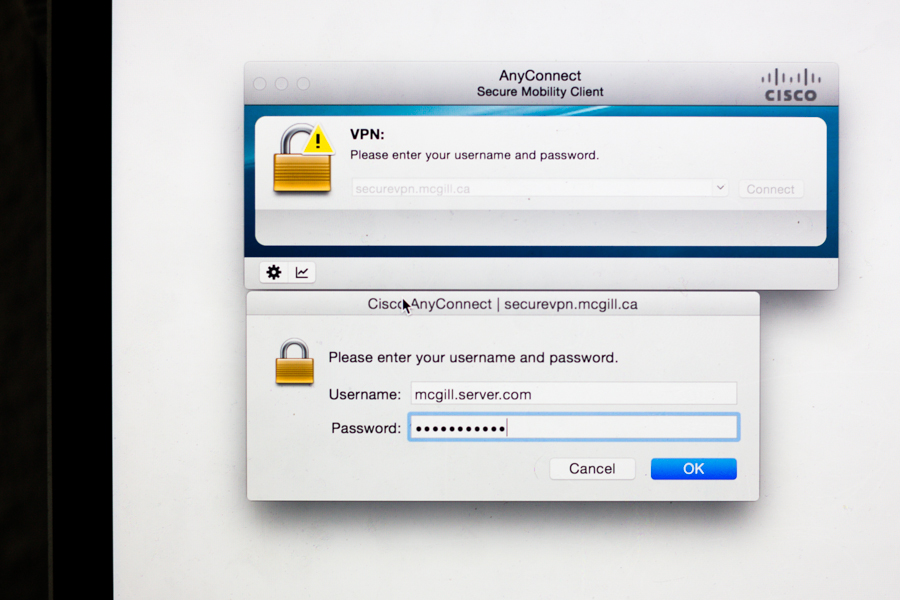
In other words, McGill’s passwords were stored in plain text. As anyone who has used McGill’s VPN will know, the password used to access that system is the same one used for email, MyMcGill, and most other McGill services.
Since student and staff passwords were stored by the VPN system in plain text, they were essentially very vulnerable to an outside attacker or a disgruntled IT Services employee who could have ran away with the data of past and present students and staff en masse. There is also a possibility that by storing passwords in plain text, McGill was violating its legal duty to “take the security measures necessary to ensure the protection” of its users’ information, as McGill is required to do by Quebec’s Act Respecting Access to Documents Held by Public Bodies and the Protection of Personal Information.
Insecure password storage is particularly ironic – and even hypocritical – given that IT Services is given to proselytizing the virtues of information security to its users.
“System security should not depend on the secrecy of the implementation or its components.” – U.S. National Institute of Standards and Technology
Roquet noted that McGill’s insecure VPN system is being phased out over the next month or two, and that the new system “uses a more secure protocol.” But just how “secure” will McGill’s new system actually be? Will it put an end to the practice of storing plain text passwords? We don’t know, and McGill won’t say. Doug Sweet, McGill’s Director of Internal Communications, told The Daily, “The University is not in the habit of discussing security measures in detail, whether it be IT security or the physical security of the campus. For obvious reasons.”
For people unfamiliar with information security, Sweet’s analogy to “physical security” might at first sound understandable: of course organizations will want to keep their security policies confidential, to avoid having people take advantage of knowledge of their inner workings.
But this approach, which is commonly referred to in the IT security industry as “security through obscurity” has been all but unanimously rejected by security experts and worldwide standards bodies alike in favour of “security through transparency.” The U.S. National Institute of Standards and Technology, for example, is clear that “system security should not depend on the secrecy of the implementation or its components.” Not only are transparent security policies more secure, but being able to verify that McGill is taking appropriate measures is what allows us as students and staff to trust that our personal information is safe in their hands. If IT Services had been transparent about its practices to begin with, it seems impossible that they would have failed to notice the vulnerabilities in their VPN system before now.
And it’s not only the information stored in our McGill accounts – sensitive as that may be – that is put at risk by plain text password storage. Because many people reuse the same passwords across different websites, if someone’s McGill password is discovered, it’s likely that this will also allow access to other accounts that belong to that same person – their Gmail or Canada Revenue Service account, for example – if the accounts were protected using the same password.
In response to the problem of insecure password storage, a website called Plain Text Offenders was launched in 2011. The site describes its motivating purpose as follows: “We’re tired of websites abusing our trust and storing our passwords in plain text, exposing us to danger. Here we put websites we believe to be practicing this to shame.“ The site allows users to post examples of companies that have been revealed to store passwords in plain text, in an attempt to shame the companies into creating more secure systems.
Unlike the mostly low-budget companies shamed by Plain Text Offenders, McGill is an institution with enormous resources at its disposal. Given the sensitivity of the information McGill passwords can unlock – not only email messages, but also employee information, student transcripts, and more – students and staff deserve a clear, explicit answer from McGill IT Services explaining what measures it is (or is not) taking to ensure that our passwords remain secure.