On June 9, former National Security Agency (NSA) subcontractor analyst Edward Snowden – a previously anonymous source – revealed himself as the whistleblower for Verizon metadata collection and the source of an even more controversial leak regarding the NSA’s top-secret intelligence program, PRISM.
Internet users around the world were outraged when they learned of the shocking allegations regarding the NSA. The initial leak revealed a top-secret order requiring Verizon Wireless, one of the United States’ largest telecom providers, to allow the NSA access to telephony metadata – daily call records of its customers – over a three-month period.
Snowden provided both the Guardian and the Washington Post with a 41-slide presentation describing PRISM and the methods used to extract information from several of the largest internet services based in the U.S. However, both newspapers only published five slides. “If you saw the slides you wouldn’t publish them,” Washington Post’s Barton Gellman tweeted, adding, “Most people would defer judgement if they didn’t know the full contents.” The released slides implicated Microsoft, Yahoo, Google, Facebook, PalTalk, AOL, Skype, YouTube, and Apple as direct information sources for the PRISM surveillance program.
While little is known about the remaining 36 slides, their leak has sparked an ongoing debate regarding the legality of the surveillance methods employed by the NSA. Discussion, both conducted in the U.S. Congress and on the internet, revolved around whether the NSA overreached its privileges after Congress passed the Patriot Act in the wake of the devastating attacks of 9-11.
Snowden’s leak is not the first time the NSA’s data collection program has appeared in mainstream media. On November 14 2012, Dennis Kucinich, a member of the U.S. House of Representatives, wrote an op-ed for the Huffington Post stating that the NSA “routinely collects 1.7 billion emails, phone calls, and communications every single day.”
It is interesting to note that although the NSA’s massive data collection was made public last year, it took Snowden’s whistleblowing to bring about a widespread and heated debate about internet security.
What is PRISM?
According to The Washington Post, PRISM (Planning Tool for Resource Integration, Synchronization, and Management) is a system used by the NSA to request private communications stored on the servers of nine popular internet services. Access to user data is governed by Section 702 of America’s Foreign Intelligence Surveillance Act (FISA), and must be authorized by the FISA Court with a secret court order. These data requests are legal, provided the NSA is at least 51 per cent certain that the target user is neither a U.S. citizen nor located within the United States.
Previous speculation on the “direct access” mentioned in the leaked slides led reporters to conclude that the NSA has direct access to companies’ servers, with full consent and cooperation on behalf of these aforementioned companies. Further information has revealed that these companies chose to develop systems where they could securely upload requested user data instead of the broad access that the NSA initially wanted. Rather than automatic access, companies only share data of specific users after legally reviewed FISA Court order requests, representing a more efficient and secure data transfer process.
Should we be concerned?
A recent Pew poll reveals that 62 per cent of Americans surveyed believe that it is important for the federal government to investigate terrorism even if it intrudes on personal privacy, compared to 34 per cent that value privacy more even if it interferes with the government’s ability to investigate terrorism. These figures are comparable to a 2006 poll where the split was 65/32, suggesting public opinion remains largely unchanged since Snowden’s leaks.
Internet users may consider communications snooping by the NSA to be benign and in their interest, but there are numerous reasons to be concerned. Richard O. Lempert, a Visiting Fellow in Governance Studies at the Brookings Foundation, professor at the University of Michigan, and former Chief Scientist and Basic Research Lead in U.S. Homeland Security, argues that future governments could use these technologies to squash dissent and target citizen movements before they even begin. In a Brookings Institution blog post on June 13, Lempert stated that these technologies combined with increasingly widespread surveillance cameras, photo recognition software, and spy drones being used domestically, as well as DNA, fingerprint, photo, and other searchable digital databases create an “infrastructure of tyranny.”
People posing no terrorist threat are likely to have nothing to fear from the NSA’s surveillance, Lempert states; however, even if the federal government authorized these programs to protect against terrorism, it would be a mistake to not question the possibility of their abuse.
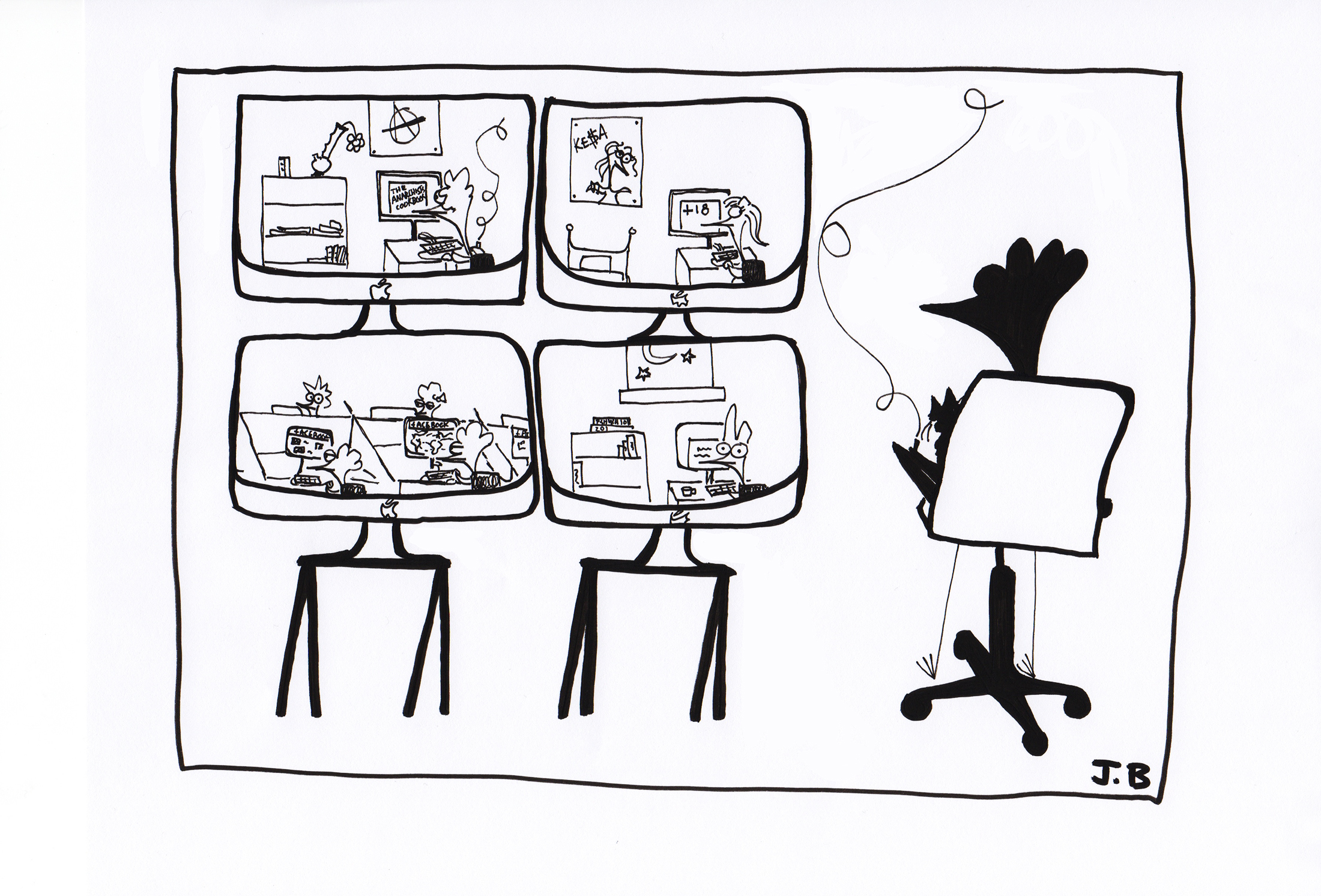
In his June 10 op-ed at the Guardian, Ian Brown, senior research fellow at Oxford University’s Internet Institute, says that the law-abiding should be very concerned about internet surveillance. He argues that by using rapidly advancing data mining technologies, corporations and government agencies can now paint a detailed picture of our lives with very little data. This should be particularly concerning in an age where people share their most intimate details over social networks such as Facebook and Twitter. Brown argues that benign activities like a call to a country earmarked by government agencies such as Pakistan doesn’t say much in itself, but combined with calls to said countries from others in your contact list, web searches for radical websites, and purchases of books found in collections of terrorism suspects, you have a pattern that may be flagged by data crunching algorithms.
Zach Beauchamp, a ThinkProgress reporter, argues against widespread monitoring of internet communications, taking inspiration from French social theorist Michel Foucault. In his June 10 article on Alternet, he uses Foucault’s illustration of philosopher Jeremy Bentham’s hypothetical Panopticon prison design to note “the omnipresent fear of being watched by the state….caused people to adjust the way they acted and even thought without ever actually being punished.” Beauchamp argues that since the NSA has revealed this hypothetical mass surveillance system as a reality, “[People will] tailor their online habits to it.”
What does this mean for Canada?
Many Canadians use web services operating from within the U.S. When registering for services from companies such as Facebook, Google, and Microsoft, individuals must agree to the company’s privacy policy and terms of use. For many sites, this often involves consent to release your personal information to the companies for the purposes of targeted advertising, but also to government agencies. All personal data as well as emails, Facebook posts, and any shared online content are likely to pass through American data networks and Internet Service Providers and are thus susceptible to seizure by presentation of a FISA court order.
The NSA is not the only government agency that collects communication metadata. Communications Security Establishment Canada (CSEC) holds a similar mandate to that of its American counterpart. According to the CBC, this involves the ability to monitor the communication of foreign persons – those who are neither Canadian citizens nor currently located within Canada.
The buzz in the Canadian media following the PRISM program leak has prompted journalists, critics, and citizens alike to question the extent to which the CSEC receives information about Canadians from partner intelligence agencies, and the likelihood that it monitors communications of Canadian citizens.
Canada is part of a multilateral intelligence sharing agreement with the U.S., New Zealand, Australia, and the United Kingdom known as the Five Eyes. In an interview with the CBC, David Skillicorn, a professor in the School of Computing at Queen’s University, stated that this [inter-agency] relationship has been carefully constructed so that countries are not delivering information regarding citizens of Five Eyes members to their respective intelligence agencies. Instead, he notes, “it’s as if the five countries’ citizens were one large, collective group, and their mutual communications are not intercepted by any in the Five Eyes community.
The secrecy concerning the details and scope of both the NSA and CSEC’s metadata harvesting program make it next to impossible to judge whether or not this surveillance is warranted or to figure out just exactly what this “Big Data” revelation means for Canadians.
Privacy? What privacy?
While the issue of digital privacy is a top priority for some internet users and internet privacy advocates, it seems that other users have not heard about the scandal, or simply do not care. Many internet users have tweeted and commented on their lack of concern for data collection if its purpose serves to preserve national security. Others claim they have no problem with the collection because they have nothing to hide.
When interviewed by The Daily, students gave their opinions on internet privacy and the NSA.
Sasha, a U2 Management student, had not heard of PRISM but said that he is generally concerned about internet privacy. “I don’t really know if I’m for or against [government surveillance],” he says, adding that “if it’s in the name of combating terrorism, I think I’m probably for it because I don’t have that much to hide myself, but I can see why it’s a sensitive issue for a lot of people.”
Omkar, a second year master’s student in Computer Science, had never heard of Snowden’s NSA leak. When explained that the NSA was collecting data on foreign citizens in the name of its national security, he replied, “It’s not okay, that’s not my national security. I’m not a U.S. citizen so I have problems with that.” He added, “If something happens to me, then I’ll look at it, but it’s remote, not very likely.”
While these surveillance technologies may be beneficial to us all, governments possess the potential for abuse if not kept in check. In order to ensure the continued protection of our democratic freedoms, there must be more stringent citizen oversight of government policies, a task only possible if we keep past and present government transgressions in mind.